With rampant unemployment ongoing, a job offer through LinkedIn can seem like a godsend. Watch out though, as some offers aren’t what they seem.
The common garden-variety phishing attack uses a technique some experts call spray and pray. Fraudsters set up a clone of some sensitive site such as an online banking website and try to trick people into logging in. It doesn’t matter if 999 people are smart enough to spot and avoid the fraud. That one in a thousand who’s distracted or foolish enough to log in is pure gold to the fraudsters. With the captured login credentials, they have total power over the compromised account. The recent LinkedIn phishing attack was nothing at all like this.
Before its attempts to morph into a full-on social media site, LinkedIn focused almost entirely on making connections and finding jobs. That high-importance contact who wouldn’t respond to your emails might become more responsive after a personal introduction by a mutual friend. And putting your resume and experience on LinkedIn means people can find you to make connections or even job offers. That’s the expectation recent attacks have targeted.
I hate to say it, but job seekers make a perfect target group. With the pandemic’s upheaval, more people than ever are looking for a job. Some are desperate. A job offer, even from an unknown source, can seem like a godsend. And an apparent connection with LinkedIn makes the offer even more tempting.
Spear Phishing Menace
Researchers in the Threat Response Unit (TRU) of security provider eSentire broke the news that a hacking group is targeting professionals with fake job offers through LinkedIn. The emails draw on each victim’s profile to create a convincing, personalized offer. My profile says I’m a Lead Analyst at PCMag. Had I been a target, the email would have contained an attachment called “Lead Analyst – position.”
This kind of targeted attack is called spear phishing, and it’s a lot harder to detect than the spray and pray technique described above. The latter might push a Wells Fargo bank link out to a huge horde of consumers, most of whom don’t even have a Wells Fargo account. A spear phishing attack is addressed to you and contains personal information, different for each target.
Sophisticated Malware Attack
What happens if you fall for the scam? Opening the job offer triggers a series of events that wind up installing a backdoor malware process called more_eggs. There’s no malicious file for an antivirus to detect. All the action takes place by subverting normal Windows processes and running scripts in memory. For those in the industry, the eSentire blog post linked above details exactly which processes are involved and how their security is breached.
Once it has settled in the victim system, the more_eggs process checks in periodically with its Command and Control website, awaiting orders. Those orders come from a hacking group that styles itself as Golden Chickens. (You can’t make this stuff up!) Just what it would have done is unknown, as the eSentire TRU team disrupted the attack system upon discovering it. According to the ThreatPost blog, previous more_eggs attacks have been used to “breach retail, entertainment and pharmaceutical companies’ online payments systems.” The Golden Chickens group planned to rent out the victim PCs in a kind of malware-as-a-service scheme, so it could have been used for almost any nefarious purpose.
Sophisticated Malware Defense
Given that more_eggs doesn’t have a presence in the file system, is it even possible for an antivirus utility to defend against it? I asked contacts at several major security companies for a quick take. Their answers were reassuring.
“Bogus job offers pointing to fake links or malicious attachment are nothing new on LinkedIn,” said Philippe Broccard, Senior Product Manager for Vipre Security. “The increase of fake LinkedIn profiles has rendered this platform extremely insecure.”
He noted that while the more_eggs malware itself is fileless, it uses a gimmicked ZIP file to get on the system, stating he “would expect Vipre to pick it up” at that point. Broccard pointed out that the attack does pose “a serious risk to any financial organization,” and suggested that any such organization could benefit from security awareness training.
“According to the information I’m seeing, the infection vector is an email ZIP attachment which contains an LNK file which triggers the file-less attack,” said Pedro Bustamante, VP of Research and Innovation at Malwarebytes. “This would be stopped by our signatureless anti-exploit technology, as part of its ‘application control and hardening’ component, which would prevent email clients from spawning the file-less command.”
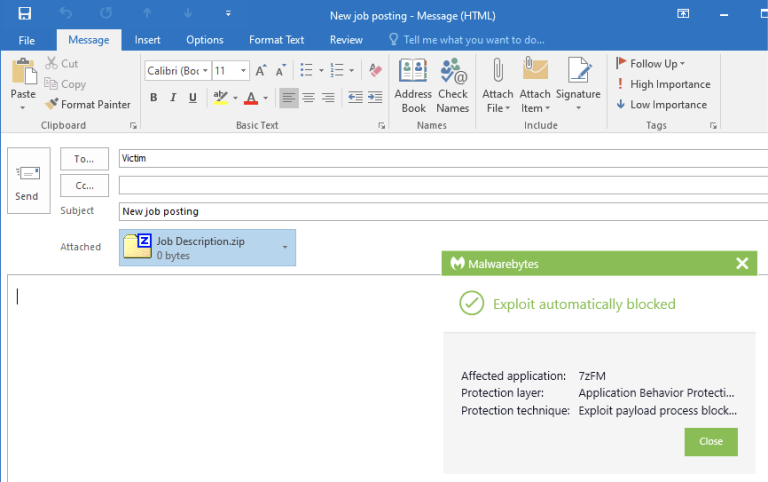
Bustamante kindly supplied a mockup of what such a blocking event would look like.
According to Denis Parinov, a Kaspersky security expert, “The described malicious software has long been known, and the backdoor dubbed more_eggs has been used by various threat actors at different times. At the same time, attacks on LinkedIn users involving a similar scheme and the malware of this family have been periodically detected, at least since 2018, with minor changes. Our products detect all the components used in such attacks.”
I’m sure these products aren’t unique in their ability to fend off more_eggs. If you’ve installed a top-tier antivirus or security suite, you should be safe from this well-known attack. But don’t get complacent; the next round of spear phishing emails might inject zero-day malware that (at least temporarily) eludes even the top security products.
Don’t Fall for Spear Phishing
It’s very difficult to know if a given email is a legitimate job offer or a spear-phishing fake. It’s not like the more common undirected phishing attack, which offers plenty of clues. If you have the slightest inkling that a job offer may be a phishing fraud, you can check in with LinkedIn’s Safety Center. If you’re just not sure, forward the message to phishing@linkedin.com or use the Possible Scam report form. Better to report a valid job offer in an excess of caution than to get suckered by a fake and malicious one.
By Neil J. Rubenking